I have had the pleasure to be on the MVP Unplugged show with Justin Garrett where I spoke about how to use AI services (yes Copilots and more) to take advantage of those great big piles of data that is your Azure Resource metrics, your application diagnostics, your security trace, and your usage cost data, and where Microsoft is going now when putting the Copilots to work in the Cloud for our benefit.
I always say this, and it bares repeting. You may think your business is large, but in Azure Cloud terms even the larger enterprise companies are but a small customer in the totality of things. That written, for Microsoft an Azure datancentre region can still on occasion run low on capacity of certain services. At the same time, Microsoft want more satisfied customers using their regions. That means for Microsoft to empower more of their customers to spend wisely and make room for even more success.
In other words; it makes business-sense for Microsoft to help their customers optimise their usage and be as effective and successful as possible on their Cloud Platform. This means that Microsoft is investing a ton in ever better tooling for their cloud consuming customers!
I want to say a hardy thank you to Justin for having me on the show which is much appreciated.
In this episode, you’ll learn:
✅ How to use Azure Monitor and Log Analytics for enterprise observability.
✅ Why Service Groups help Azure understand application architecture.
✅ How AI-assisted investigation accelerates root cause analysis.
✅ Best practices for managing diagnostics data at scale.
✅ How Azure Copilot turns natural language into KQL queries.
✅ When to use Azure Advisor insights to optimize performance and cost.
Please enjoy this episode of MVP Unplugged:
Some photos from the show:
Fun snap… the size of that fish!
Original post on YouTube: Taming the Data Estate with Copilot and Azure Service Monitor | MVP Unplugged
The whole MVP Unplugged playlist: MVP Unplugged - YouTube
Join host Justin Garrett from the Microsoft MVP Program as he sits down with Magnus Mårtensson, a 14-time Azure MVP, to explore what it takes for enterprises to manage growing data estates with AI-powered observability in Azure. As organizations scale across hybrid environments, multi-cloud platforms, and legacy systems, monitoring application health and managing diagnostic data becomes increasingly complex. In this episode, Magnus explains how Azure Monitor, Service Groups, and AI-assisted investigation are transforming observability by turning massive volumes of telemetry into actionable insight.
You’ll learn how Azure Copilot can analyze logs, detect anomalies, recommend next steps, and help prioritize Azure Advisor recommendations using natural language inside tools like Visual Studio Code. The result: faster investigations, improved uptime, reduced operational overhead, and smarter decision-making across your cloud estate. Whether you're modernizing applications or optimizing resources across subscriptions, this episode highlights real-world strategies for building resilient, cost-efficient systems with AI in Azure.
00:06 - Welcome to MVP Unplugged Episode 3
00:32 - Meet Magnus Mårtensson
01:24 - Observability Challenges Explained
03:14 - Azure Monitor Overview
05:27 - Managing Log Data at Scale
06:21 - AI for Diagnostics Data
09:36 - Azure Service Groups (Preview)
11:04 - Demo: Mapping Applications
15:20 - Health Models
21:30 - AI-Assisted Investigation
27:30 - Azure Copilot in VS Code
30:33 - Azure Advisor with AI
35:35 - AI for Cost Optimization
39:23 - Wrap-Up
#AzureMonitor #AzureCopilot #Observability #EnterpriseIT #LogAnalytics
#CloudComputing #AIinCloud #MicrosoftDeveloper #Azure #DevOps
#ApplicationMonitoring #CloudOptimization #MVPUnplugged
Resources & Links
Free Microsoft Foundry Trial: https://aka.ms/devrelft
✏️ Azure Monitor docs: Azure Monitor documentation - Azure Monitor | Microsoft Learn
✏️ Azure Service Groups docs: Azure Service Groups documentation | Microsoft Learn
➡️ Azure Tools for VS Code: Getting Started with Azure Tools for Visual Studio Code
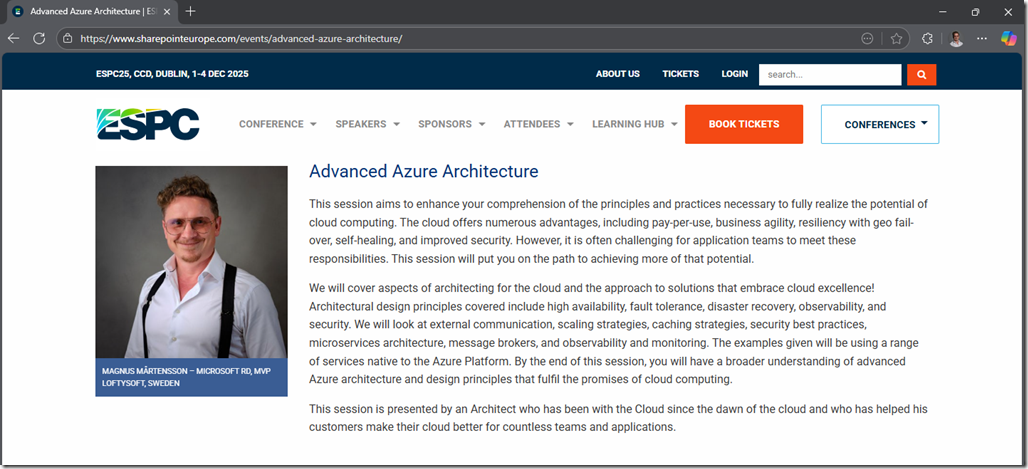
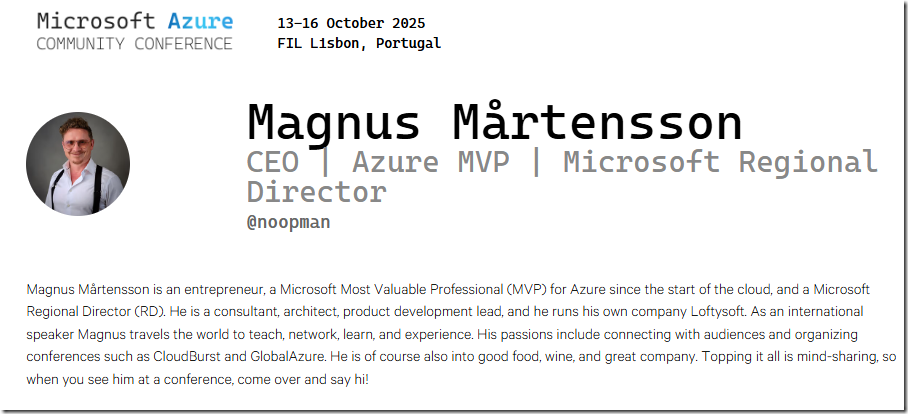
About Magnus:
Magnus Mårtensson is a cloud architecture advisor and founder of Loftysoft, helping organizations design scalable, cloud-native solutions aligned to business strategy. He is an internationally recognized speaker, trainer, and community leader behind events like CloudBurst and Global Azure.
About Justin:
Justin Garrett is host of MVP Unplugged and a Principal PM in Developer Relations at Microsoft, with 20+ years of experience across Windows, Bing, Edge, and Cloud Advocacy. He also leads the Microsoft MVP Program.